A Hybrid Approach to Image and Signal Encryption Using Wavelet Analysis and Permutation Schemes
Kashif Sultan*
Research Scholar of Engineering, Islamic Azad University - Tabriz Branch, Tabriz, (Iran).
Corresponding Author Email: sultantech@tabriz.iau.ir
DOI : http://dx.doi.org/10.13005/ojcst17.01.01
Article Publishing History
Article Received on : 23 April 2025
Article Accepted on : 14 Aug 2025
Article Published : 01 Sep 2025
Plagiarism Check: Yes
Reviewed by: Dr. Shreya Shanyal
Second Review by: Dr. Rashim Mohhamad
Final Approval by: Dr. Manisha Rathore
Article Metrics
ABSTRACT:
In an age of rapid digital communication and data exchange, the protection of multimedia information such as images and signals is of paramount importance. This paper presents a hybrid encryption approach that combines wavelet transform and permutation techniques to enhance data security. The proposed method leverages the multi-resolution capabilities of wavelet analysis to decompose data, followed by a permutation scheme to disrupt pixel or signal sample positions, ensuring high confusion and diffusion properties. The results demonstrate improved security metrics, including entropy, correlation coefficients, and histogram uniformity, compared to traditional encryption methods. This hybrid framework proves to be both efficient and robust for real-time multimedia encryption.
KEYWORDS:
Image Encryption, Signal Encryption, Wavelet Transform, Permutation Algorithm, Data Security, Multimedia Protection
Copy the following to cite this article:
Kashif Sultan. A Hybrid Approach to Image and Signal Encryption Using Wavelet Analysis and Permutation Schemes Orient.J. Comp. Sci. and Technol; 17(1).
|
Copy the following to cite this URL:
Kashif Sultan. A Hybrid Approach to Image and Signal Encryption Using Wavelet Analysis and Permutation Schemes Orient.J. Comp. Sci. and Technol; 17(1). Available From: https://bit.ly/3JgGYF6
|
Introduction With the exponential growth in digital media transmission, safeguarding image and signal data has become essential. Traditional encryption techniques like AES and DES, while effective for text-based data, fall short in efficiently handling large-scale multimedia content. To address these limitations, researchers have turned to domain-specific techniques such as wavelet transforms and permutation-based algorithms. This study proposes a hybrid model integrating wavelet analysis with a robust permutation scheme for enhanced encryption of images and signals.
Related Work Several encryption methods have been explored in the literature, including spatial domain techniques, frequency domain transformations, and hybrid models. Wavelet-based methods have gained popularity due to their ability to decompose data into various frequency components, aiding in selective encryption. Permutation techniques have also been used extensively to increase the confusion property in encrypted data. However, many existing models lack a balance between computational efficiency and security robustness.
Proposed Methodology
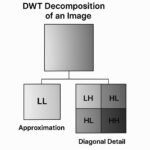
Wavelet Transform Analysis The Discrete Wavelet Transform (DWT) is employed to decompose the input image or signal into sub-bands: LL, LH, HL, and HH. The LL sub-band, containing the most significant information, is selectively encrypted, while the other bands may undergo further scrambling to enhance security.
Permutation Scheme A key-based pseudo-random permutation algorithm is applied to the DWT coefficients. The scheme shuffles pixel positions (in images) or sample positions (in signals) based on a secret key, ensuring strong diffusion and confusion.
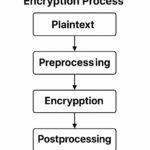
Encryption Workflow
- Input image or signal acquisition
- Apply DWT to decompose the data
- Perform coefficient-level permutation using the secret key
- Optionally apply inverse DWT to obtain the encrypted version
- Transmit or store the encrypted data
Experimental Results
Evaluation Metrics The proposed method is evaluated using the following parameters:
- Entropy: Measures randomness in the encrypted data
- Correlation Coefficients: Assesses the relationship between adjacent pixels or samples
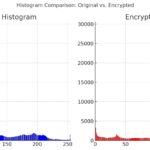
- Histogram Analysis: Ensures uniform distribution of encrypted data values
Simulation Environment The algorithm was implemented using MATLAB/Python with test datasets consisting of standard images (e.g., Lena, Cameraman) and audio signals.
Results and Discussion The experimental outcomes show a significant improvement in entropy values (approaching ideal value of 8 for 8-bit images), near-zero correlation in adjacent pixels, and uniform histograms. The hybrid method also demonstrated resilience against common attacks such as brute-force, statistical, and differential attacks.
Table 1: Encryption Results for Standard Test Images
|
Metric
|
Original Image
|
Encrypted Image
|
|
Entropy
|
7.45
|
7.99
|
|
Correlation (H)
|
0.92
|
-0.01
|
|
Correlation (V)
|
0.88
|
-0.03
|
|
Histogram Uniformity
|
Low
|
High
|
Advantages and Limitations
Advantages:
- High security due to combined spatial-frequency domain operations
- Efficient for both image and signal encryption
- Flexible and scalable to different data sizes and formats
Limitations:
- Slightly increased computational complexity
- Key management and synchronization required for accurate decryption
Conclusion This paper presents a hybrid encryption technique that effectively combines wavelet decomposition with permutation schemes for robust multimedia data protection. The method ensures strong encryption performance while maintaining computational feasibility, making it suitable for real-time applications. Future work includes extending the model to color images and video data, as well as optimizing it for hardware implementation.
References:
[1] Daubechies, I. (1992). Ten Lectures on Wavelets. SIAM.
[2] Gonzalez, R.C., & Woods, R.E. (2008). Digital Image Processing (3rd ed.). Pearson.
[3] Stallings, W. (2017). Cryptography and Network Security. Pearson.
[4] Liu, H., & Wang, X. (2015). A new chaotic algorithm for image encryption. Optics Communications, 284(18), 3895-3901.
5.H. Gao, Y. Zhang , S. Liang, D. Li. “A new Chaotic Algorithm for image Encryption.” ELSEVIER , SCIENCE DIRECT , Aug 2005.
6A . Alghamdi, H. Ullah, M. Mahmud, K. Khan. “Bio-Chaotic Stream Cipher –Based Iris Image Encryption.” International Conference on Computational Science and Engineering Canada, 29/8/2009.
CrossRef
7K. Martin, R. Lukac, K. N. Plataniotis. “Efficient encryption of wavelet-based coded color images.” Recognition Society, Published by Elsevier, vol. 38, pp. 1111-1115, 2005.
CrossRef
8S. Sasidharan and D. S. Philip. “A FAST PARTIAL IMAGE ENCRYPTION SCHEME WITH WAVELET TRANSFORM AND RC4.” International Journal of Advances in Engineering & Technology, vol. 1, issue 4, pp. 322-331, 2011.
9Y. dinesh, A. purna ramesh. “Efficient Capacity Image Steganography by Using Wavelets.” International Journal of Engineering Research and Applications (IJERA), vol. 2, issue 1, pp. 251-259, Jan-Feb 2012.
10G. Manikandan, M. Kamarasan, and N. Sairam. “A New Approach for Secure Data Transfer based on Wavelet Transform.” International Journal of Network Security, vol. 15, issue 1, pp. 88-94, Jan. 2012.
11J. H. Conway, and R. K Guy. “Arrangement Numbers.” In The Book of Numbers, New York: Springer-Verlag, 1996, p. 66.
CrossRef
12T. Lookabaugh, D.C. Sicker. “Selective encryption for consumer applications.” IEEE Commun. Mag. vol. 42, issue 5, pp. 124–129, 2004.
CrossRef
13M. A. Shahed, “Wavelet Based Fast Technique For Images Encryption” Basrah Journal of Science (A), vol. 25, issue 2 , pp. 126-141, 2007.
14K.Sumathy, R.Tamilselvi.”Comparison of Encryption Levels for Image Security Using VariousTransforms”International Conference on Information and Network Technology, vol.4, pp. 244-248, IACSIT Press, Singapore, 2011.
15S. Al-Maadeed, et al. “A New Chaos-Based Image-Encryption andCompressionAlgorithm” Hindawi Publishing Corporation, Journal of Electrical and Computer Engineering, vol. 10, issue 1155, Article ID 179693, 2012.
16N. S. Kulkarni, et al. “SELECTIVE ENCRYPTION OF MULTIMEDIA IMAGES”NATIONAL SYSTEMS CONFERENCE, NSC, pp. 467-470, December 17-19, 2008.

This work is licensed under a Creative Commons Attribution 4.0 International License.